Banks and governments race to upgrade encryption before quantum computers become powerful enough. What timelines does the security community set?
📖 Read more: Quantum Internet: How the Next Generation Web Will Work
🔓 Why Banking Encryption Is at Risk
Every time you type your password into web banking, a mathematical algorithm protects the transaction. The RSA and ECC (Elliptic Curve Cryptography) algorithms, which form the backbone of modern digital security, rely on a simple fact: multiplying two enormous prime numbers is easy, but the reverse process — factorization — is computationally impossible for classical computers. A classical supercomputer would need billions of years to crack an RSA-2048 key.
In 1994, mathematician Peter Shor published a quantum algorithm that can factorize large numbers in polynomial time. This means a sufficiently powerful quantum computer could break RSA, ECC, and DSA — essentially every public-key algorithm used by the banking sector today. According to Wikipedia, as of 2026 quantum computers still lack enough processing power to break widely used cryptographic algorithms. But that could change sooner than many expect.
🕵️ Harvest Now, Decrypt Later: The Silent Threat
Perhaps the most alarming aspect of the quantum threat lies not in the future, but in the present. The “Harvest Now, Decrypt Later” (HNDL) strategy implies that adversaries are already recording encrypted data with the intention of decrypting it later, when they gain access to quantum computers.
For the banking sector, this is particularly critical. Financial data — account numbers, transaction histories, confidential agreements — must remain confidential for decades. Similarly, in the healthcare sector, quantum cryptography can protect electronic records for periods of up to 100 years, according to research by Stebila, Mosca & Lütkenhaus (2010). The transition must begin now, even if “Q-Day” is years away.
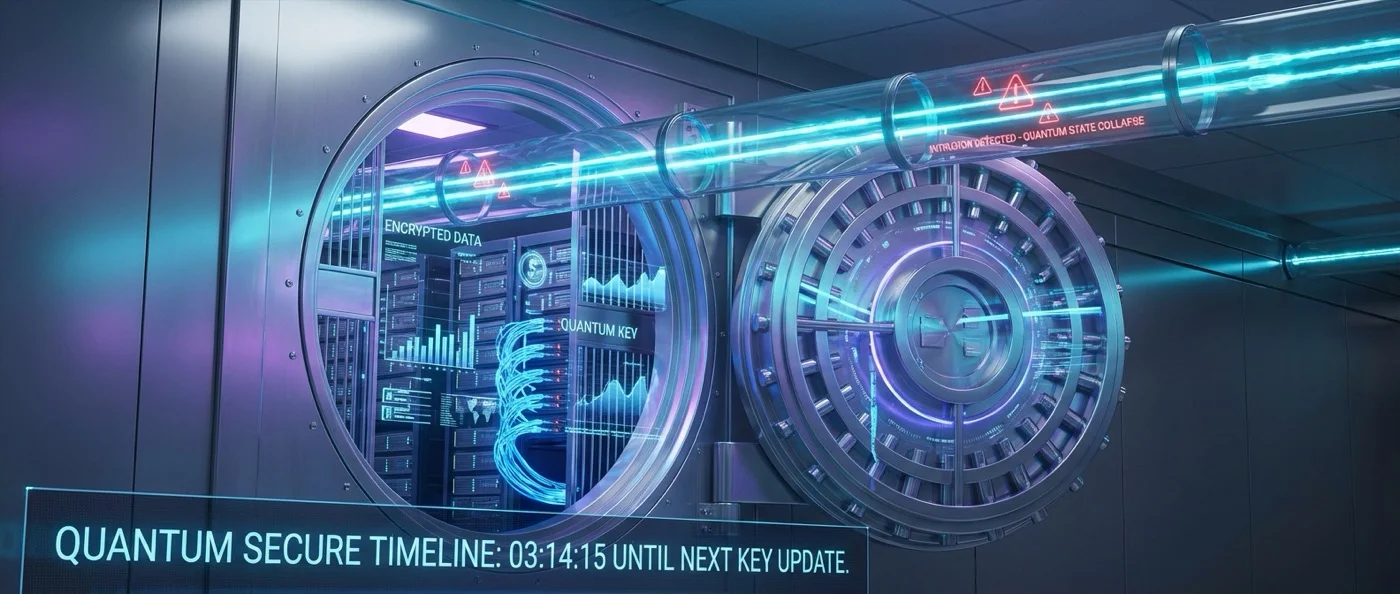
🔑 Quantum Key Distribution (QKD)
The first line of defense from the quantum world is Quantum Key Distribution (QKD). The idea relies on fundamental laws of quantum mechanics: the impossibility of cloning (no-cloning theorem) and the unavoidable disturbance during measurement.
The first QKD protocol, known as BB84, was developed in 1984 by Charles H. Bennett (IBM) and Gilles Brassard (University of Montreal). In BB84, information is encoded in non-orthogonal quantum states — photon polarizations — and any eavesdropping attempt measurably alters the data, immediately revealing the intruder. In 1991, Artur Ekert proposed an alternative approach (E91) based on quantum entanglement and Bell inequalities.
The first bank money transfer using QKD was carried out in 2004 in Vienna, with technology from Geneva-based ID Quantique. In 2007, elections in the canton of Geneva used QKD for transmitting voting results. Major QKD networks operate today in many countries: the DARPA QKD Network in the US, the Tokyo QKD Network (with NEC, Toshiba, ID Quantique collaboration), Chinese networks, and Singapore's National Quantum-Safe Network Plus (NQSN+).
Why QKD Alone Is Not Enough
Despite its theoretical security, several government agencies — the NSA (US), ENISA (EU), NCSC (UK), ANSSI (France), BSI (Germany), and ASD (Australia) — recommend alternatives. The NSA identifies five key problems: (1) QKD is a partial solution — it provides confidentiality but not source authentication, (2) it requires specialized equipment and dedicated optical fibers, (3) it increases infrastructure costs and insider-threat risks due to trusted relays, (4) practical security depends on hardware, not just physics, and (5) it increases the risk of denial of service (DoS), since cutting a single fiber suffices to disrupt communication.
📖 Read more: Quantum Chemistry: How We'll Discover New Drugs Faster
🛡️ Post-Quantum Cryptography: The Practical Solution
Post-Quantum Cryptography (PQC) represents the most realistic solution for the banking sector. These are algorithms that run on classical computers but are designed to withstand quantum attacks. No special hardware is needed — only software updates.
Research focuses on six directions: lattice-based cryptography, multivariate cryptography, hash-based cryptography, code-based cryptography, isogeny-based cryptography, and symmetric key resistance. In August 2024, NIST (National Institute of Standards and Technology) published the first three PQC standards:
• FIPS-203 (ML-KEM / CRYSTALS-Kyber): Lattice-based key encapsulation mechanism
• FIPS-204 (ML-DSA / CRYSTALS-Dilithium): Lattice-based digital signatures
• FIPS-205 (SLH-DSA / SPHINCS+): Hash-based digital signatures
• FIPS-206 (FN-DSA / Falcon): Additional signature standard (under finalization)
Particularly important for banks: the ML-KEM (Kyber) algorithm offers relatively small keys — 1,312 bytes for a public key — while maintaining high security. By comparison, McEliece (code-based) offers a key of ~1 MB, practically unsuitable for everyday banking transactions. Symmetric cryptosystems like AES-256 are already considered quantum-resistant — Grover's algorithm reduces security to the square root, transforming 256 bits to an equivalent 128 bits, which remain sufficient.
⚙️ Hybrid Model and Practical Transition
Many organizations today choose a hybrid approach: combining classical cryptography with PQC, so that even if one of the two layers is proven vulnerable, the other continues to protect. Google used hybrid cryptography in TLS tests in 2019, while Apple introduced PQ3 and Signal introduced PQXDH — protocols that integrate PQC into existing messaging infrastructures.
In June 2025, the European Union published a coordinated transition roadmap to PQC, acknowledging that the transition will take years and must begin now. The financial services industry follows: the X9 organization, responsible for security standards in financial services, is working on PQC Readiness and Crypto-Agility guidelines, while the Open Quantum Safe (OQS) project, active since 2016, develops the liboqs library — an open-source tool that integrates PQC algorithms into OpenSSL.
⏳ How Far Are We from “Q-Day”?
No one knows exactly when a quantum computer will be able to break RSA-2048. Estimates range from the 2030s to the 2040s or later. There is also the recent development by Oded Regev (2025), who published a more efficient quantum factoring algorithm, potentially reducing the number of qubits required.
Regardless of the timeline, the cybersecurity community agrees: the transition must begin now. The complexity of updating millions of ATMs, POS terminals, banking applications, core banking systems, and interbank protocols (SWIFT, SEPA) is enormous. Every year of delay increases the risk — especially considering the “harvest now, decrypt later” attacks that are likely already happening.